A system is secure when all its components are secure, that is, they perform their function by preventing attackers from gaining access to the internal parts of the system. In fact, unauthorized access can cause damage, data theft and other malicious activities.
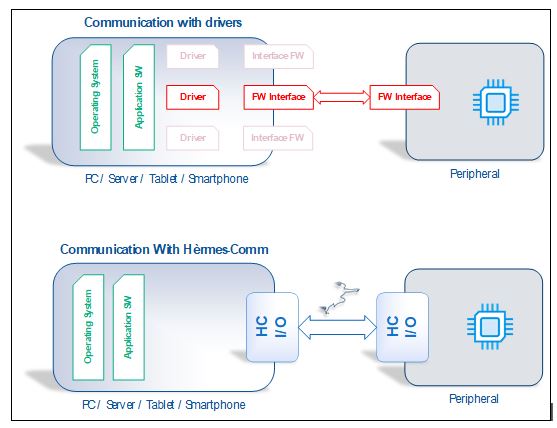
A system is typically controlled by a computer with management software (organized in several layers) and by a hardware that executes its commands: the communication between computer programs and external hardware devices (peripherals) takes place through the software driver. “Drivers” are particularly complex and expensive software programs to develop.
But not only that: they are “attackable”. New security holes are discovered every day in server programs, PC and Web applications, and mobile apps – these holes can be used to cause major damage. The most dangerous flaws are precisely those concerning the driver, because they allow access to the deeper functionalities of the Operating System, which allow the attacker to assume full access to the machine.
What is a driver
Printers, scanners, keyboards, mice, cameras, webcams, monitors, modems, sound, video and network cards, and any other kind of hardware, require drivers to communicate with computer software.
A driver is therefore the software layer used for communication between the Operating System and a device (external or internal) with which the computer must communicate. The driver works as an interpreter between the Operating System and the Hardware connected to the computer.
Drivers are specific to each operating system – for example, a driver for a printer can work in Windows 7 but not in Windows 10 (or vice versa).
The driver is a weakness
Drivers are complex and expensive to make as they are “executed” by a special component of the Operating System, called the Kernel. This is the “closest” layer to the computer hardware and has unlimited access to the entire system. The development of a driver requires specialized programming languages and consequently requires designers and developers with specialized knowledge.
Most people think that an Operating System, such as Windows, is used only for Servers or PCs: however, these are not the only devices that run an Operating System. Operating Systems are also widespread in the world of automatic teller machines (ATMs), POS terminals, Self-Service kiosks, medical systems, and many other specialized equipment. Some are particularly critical, such as the military.
All these devices are complex and expensive to upgrade compared to a normal PC because they are used in industries and environments that require lengthy testing and certification. In these cases, the drivers are therefore rarely updated, and their vulnerability opens all the ports of the system to the attacker. This can result in service interruptions, major problems, and major financial losses.
Usefulness of Hèrmes-Comm®
The Hèrmes-Comm® technology allows you to connect any hardware (peripheral, circuit, board, …) to the computer software (Server, PC, Smartphone, Tablet, circuit) without the need to install drivers, making it simpler, faster and above all secure. It eliminates the need to install the device driver and does not require special protocols, as it takes advantage of features available in each Operating System.
- Communication with the hardware takes place using the file system driver, which necessarily exists in all operating systems to manage mass memories.
- The specialized intelligence of the driver (knowledge of the communication details of the device) is incorporated into the application software.
Why Hèrmes-Comm® makes the system secure
The program that communicates with a Hèrmes-Comm® peripheral contains the necessary communication functions, including those normally performed by the driver. It allows to reach high levels of security because:
- The communication program is not run in the “Kernel” but at the “user” level, so its possible compromise does not allow access to the entire system.
- It can be written in any programming language, avoiding those complexities that can insert weaknesses in the software.
- The communication with the peripheral is protected with a patented communication protocol, which does not allow the intercepting of the exchanged data.
- The peripheral can be uniquely identified and protected with digital signature techniques using a method derived from the basic Hèrmes-Comm® patent.
Cases of attacks on drivers
Attacks on complex and specialized systems that target the driver to access the entire system are increasingly frequent. Below, by way of example, we report references of attacks to ATM systems which, using various peripherals within them, offer a greater attack surface.
https://www.bankinfosecurity.com/unsecure-drivers-allow-for-easy-windows-hacking-report-a-12909
https://reaqta.com/2020/03/attackers-are-starting-to-exploit-vulnerable-drivers-are-defenders-ready/
https://www.securityweek.com/driver-vulnerabilities-facilitate-attacks-atms-pos-systems
0 comments on “Driver software and security – The Hermes-Comm Technology”