Malware, malicious software, or a malicious computer worm, is any software intentionally designed to cause damage to a computer, server, client, computer network, or a piece of equipment. An example is Stuxnet, a malicious computer worm first uncovered in 2010 and thought to have been in development since at least 2005. Stuxnet targets supervisory control and data acquisition systems. It is, to all effects, a cyberweapon.
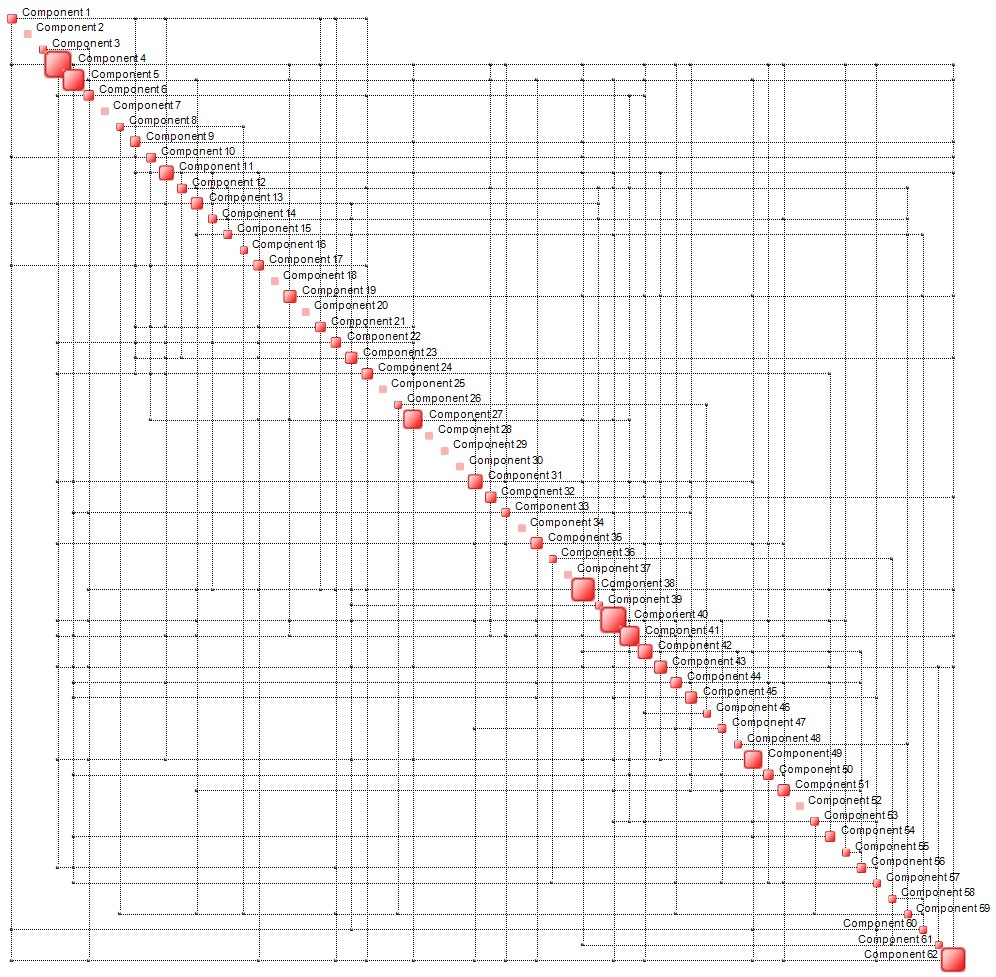
QCM technology can be used to augment conventional malware, expecially when highly complex IT systems, with a large number of components or subsystems are targeted. Malware is typically designed to hit a particular component. However, in cases, such as the one shown below – this is a small example with 60+ components – it may be a good idea to consider a different type of strike.
Highly complex systems, such as networks, or mobile platforms, are rarely in a state of equilibrium or steady state. In such cases, a worm may be designed to access QCM-generated information and hit critical components of the system for maximum damage – the large boxes on the diagonal of the complexity map. In essence, a QCM module may be incorporated into the malware and, once triggered, determine when and where to unleash the actual worm. The best time to strike is when the complexity of the targeted system is maximum – this guarantees fastest damage propagation – and the best component to attack is one of the drivers of complexity. The animation below illustrates the concept. The best time to deliver the strike is when the map appears to have the highest density and the best targets are the red discs – the complexity hubs. (NB, density of the map is not a good proxy of complexity and is mentioned here only because visually it may be more intuitive to imagine a parallel between the two.)
The approach described in this blog is, for obvious reasons, presented in extremely simplified form.

Reblogged this on muunyayo .
LikeLike